The one command-line proxy and TLS trust fix for CLIs on macOS.
Tired of CLI tools failing with certificate errors behind corporate proxies? This automated suite detects your proxy configuration, extracts internal CAs from Keychain Access, and configures all CLI tools to work seamlessly with corporate network security. Run one command and forget about SSL_CERT_FILE, proxy variables, and certificate verification errors.
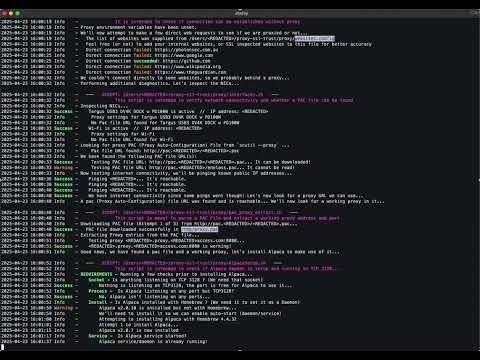
The following command will download the suite of tools to ~/Applications/proxy-ssl-trust. It will then execute the default option, equivalent to running ./Proxy_SSL_Trust.sh --proxy, which configures macOS CLI to use a proxy and PAC file, and addresses SSL trust issues.
/bin/zsh -c "$(curl -fsSL https://raw.githubusercontent.com/Enelass/proxy-ssl-trust/refs/heads/main/lib/download_run_me.sh)"~/Applications/proxy-ssl-trust/Proxy_SSL_Trust.sh [OPTION]...--help, -h: Show the help menu.--version, -v: Show the version information.--list, -l: List all the signing Root CAs from the macOS Keychain Access. This is useful to check what Root CAs are supplied or performing SSL Inspection.--scan, -s: Scan for PEM Certificate Stores on the system without patching. Useful to locate software certificate stores.--var: Set default shell environment variable to a known PEM Certificate Store containing internal and Public Root CA. Useful for quick fixes in user context.--var_uninstall: Revert any changes made by--var, restoring the original state.--patch, -p: Patch known PEM Certificate Stores (requires--scan). Useful for patching known certificate stores (not recommended).--patch_uninstall: Revert any changes made by--patch, restoring the original state.--proxy: Set up proxy and PAC file & install Alpaca as a daemon (DEFAULT).--proxy_uninstall: Uninstall proxy and PAC settings.
-
Show Help Menu:
./Proxy_SSL_Trust.sh --help
-
Show Version Information:
./Proxy_SSL_Trust.sh --version
-
List Root CAs from Keychain Access:
./Proxy_SSL_Trust.sh --list
This is an alias for
./SSL/Keychain_InternalCAs.sh -
Scan for PEM Certificate Stores:
./Proxy_SSL_Trust.sh --scan
This is an alias for
./SSL/PEM_Scan.sh -
Set Environment Variable for Certificate Store:
./Proxy_SSL_Trust.sh --var
This is an alias for
./SSL/PEM_Var.sh -
Patch Known PEM Certificate Stores:
./Proxy_SSL_Trust.sh --scan ./Proxy_SSL_Trust.sh --patch
Note: Requires running --scan first to identify certificate stores. For testing only (not recommended).
-
Set up Proxy and PAC File:
./Proxy_SSL_Trust.sh --proxy
This is an alias for
./proxy/connect_noproxy.sh
Log files are created in /tmp directory with the name Proxy_SSL_Trust.log.